AT&T reset account passwords for millions of customers this week after acknowledging a massive data breach that affected more than 73 million users.
The telecommunications giant said the leaked data set appears to be from 2019 or earlier, and affects about 7.6 million current AT&T account holders and 65.4 million former account holders.
The leaked data set includes names, home addresses, phone numbers, Social Security numbers and dates of birth, as reported by TechCrunch.
A security researcher who analyzed the data set discovered that it contained encrypted passcodes, prompting the operator to initiate a reset process, according to the outlet.
The revelation comes a week after the airline denied a breach of its systems and said there is “no indication of a compromise.”

AT&T reset account passwords for millions of customers this week after acknowledging a massive data breach that affected more than 73 million users.
The telecommunications giant said the leaked data set appears to be from 2019 or earlier, and affects about 7.6 million current AT&T account holders and 65.4 million former account holders. Pictured: A hacker posted what he claimed were 70 million AT&T records on a forum in August 2021.
AT&T customer account access codes are four-digit numbers used to access users’ accounts, either online or in retail stores.
In a statement issued on Saturday, AT&T said: ‘AT&T has launched a robust investigation supported by internal and external cybersecurity experts.
“Based on our preliminary analysis, the data set appears to be from 2019 or earlier, and affects approximately 7.6 million current AT&T account holders and approximately 65.4 million former account holders.”
“AT&T has no evidence of unauthorized access to its systems that resulted in the exfiltration of the data set,” the statement said.
The company added that “it is not yet known whether the data in those fields comes from AT&T or one of its providers.”
The shocking revelation comes after a data vendor dumped massive rolls of purported AT&T customer records on a cybercrime forum earlier this month.
The data set contains 73 million records, including 49 million unique email addresses, 44 million social security numbers and 43,000 birth dates, according to Troy Hunt, a security researcher.
After obtaining a copy of the data set and analyzing it, Hunt said in a blog post that the leaked data was real.
The researcher, owner of the data breach reporting site Have I Been Pwned, asked his subscribers if they were AT&T customers and the data seemed accurate.
Users have since come forward and said the leaked data did indeed contain their personal information, Hunt said.


The leaked data set includes names, home addresses, phone numbers, Social Security numbers and dates of birth, according to security experts who analyzed the data.


In 2023, AT&T suffered data breaches, including in March, when the company notified nine million people about the cyberattack.
One response Hunt received reads: “That’s my information.” I’m an AT&T customer,’ and someone else says, ‘Unfortunately, that seems okay.’ I was an AT&T customer in 2014, but not anymore.”
At the time, AT&T spokesman Stephen Stokes did not confirm whether the alleged data set was valid and how it spread online.
He wrote in a statement: ‘We have no indication that our systems are compromised. In 2021 we determined that the information offered in this online forum did not appear to come from our systems.
“This appears to be the same data set that has been recycled several times on this forum.”
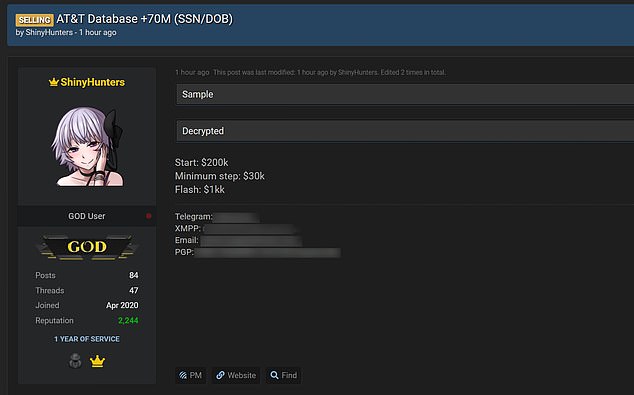
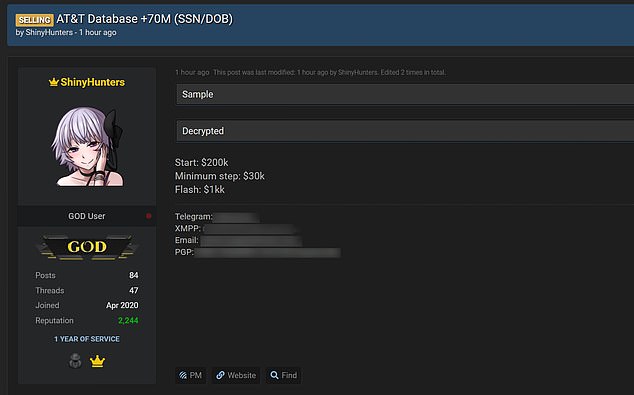
Rumors about the AT&T data breach emerged three years ago when a hacker posted what he claimed were 70 million AT&T records on a forum in August 2021.
According to Hunt, the person, known as ShinyHunters on the forum, has a proven track record of breaching large organizations.
The person attempted to sell the database with an initial price of $200,000 and incremental offers of $30,000. The hacker also said that they were willing to sell it immediately for $1 million.
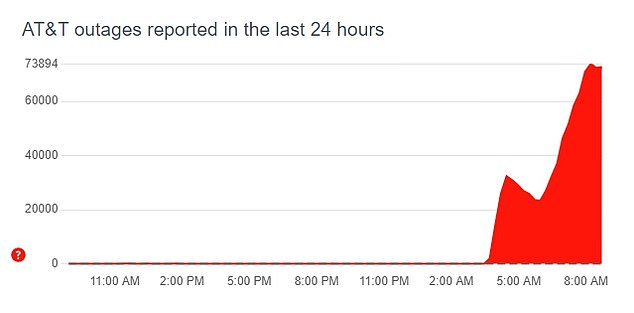
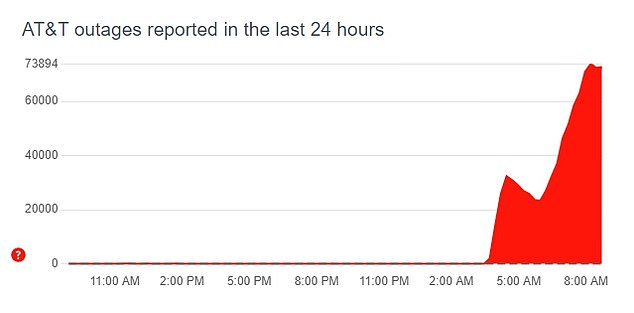
In February of this year, 70,000 users were left without a telephone signal for hours during a massive blackout
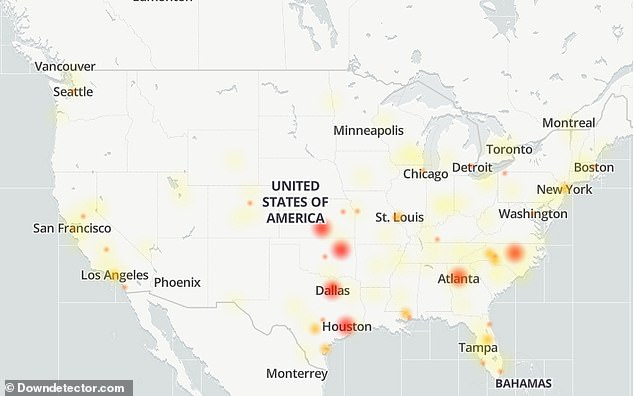
The company attributed the outage to a ‘software update failure’ while it was expanding its network coverage.
In 2023, AT&T suffered data breaches, including in March, when the company notified nine million people about the cyberattack.
The company blamed a third-party vendor that was attacked by hackers in January and said its own system was not compromised.
In February of this year, 70,000 users were left without a phone signal for hours during a massive blackout.
The company attributed the outage to a “software update failure” while it was expanding its network coverage.
However, there has been speculation that the problem could have been the result of a cyber attack.
Cyber experts also told DailyMail.com that the issue had characteristics of a cyber attack, potentially an attempt by hackers to blackmail the company or steal user data.
Although the company insisted there was “no indication of malicious activity,” both the Federal Bureau of Investigation (FBI) and the Department of Homeland Security (DHS) were looking into what disrupted the service.