<!–
<!–
<!– <!–
<!–
<!–
<!–
A BBC Sounds podcaster has lifted the lid on the possibility of dating during the holy month of Ramadan.
Presenter of BBC doesn’t even sound like water Mehreen Baig and her guest Big Zuu, both Muslims, were interviewed by Radio 1 DJ Jamie Laing in a recent episode of the Ramadan Guide podcast.
In the UK, some three million Muslims celebrate Ramadan – which marks the month when the Quran was first revealed to the Prophet Muhammad – via fasting from food and drink during the day.
In the show, Laing, 35, reads the question: “Are you allowed to go out with people during Ramadan?”
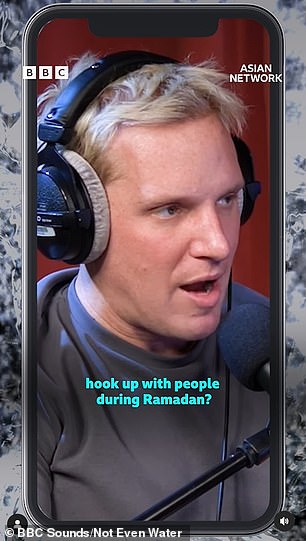
During a recent episode of Not Even Water, a guide to Ramadan on BBC Sounds, Radio 1 presenter Jamie Laing asked the show host if he was willing to go out with him for the holy month.


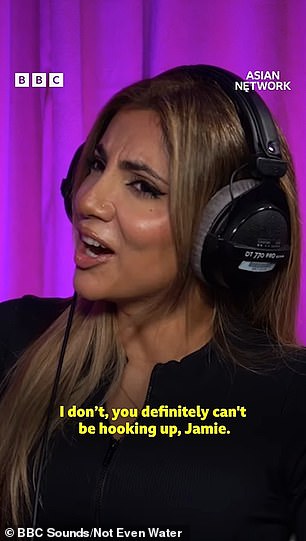
The presenter, who left her BBC Asian Network Saturday show last month, hosts the series, which aims to provide an insight into Ramadan.
Baig, who is also behind review series Glow up your Grades, told the former Made in Chelsea star: “I say no. I vote no. You definitely can’t date Jamie.
Big Zuu clarified by saying, “Obviously, during the holy month, committing sin is wrong, but we are human. So if you associate your babies, it’s wrong. But you’re not the worst human in the world.
BBC presenter Baig, who last month quit her Saturday show on the BBC Asian Network, later shared her thoughts, saying: “Refrain. We should monitor our interactions with the opposite sex, even if it is not Ramadan.
According to the rules of the Quran, a couple should only have sex after the end of the day during the holy month, and only if they are husband and wife.
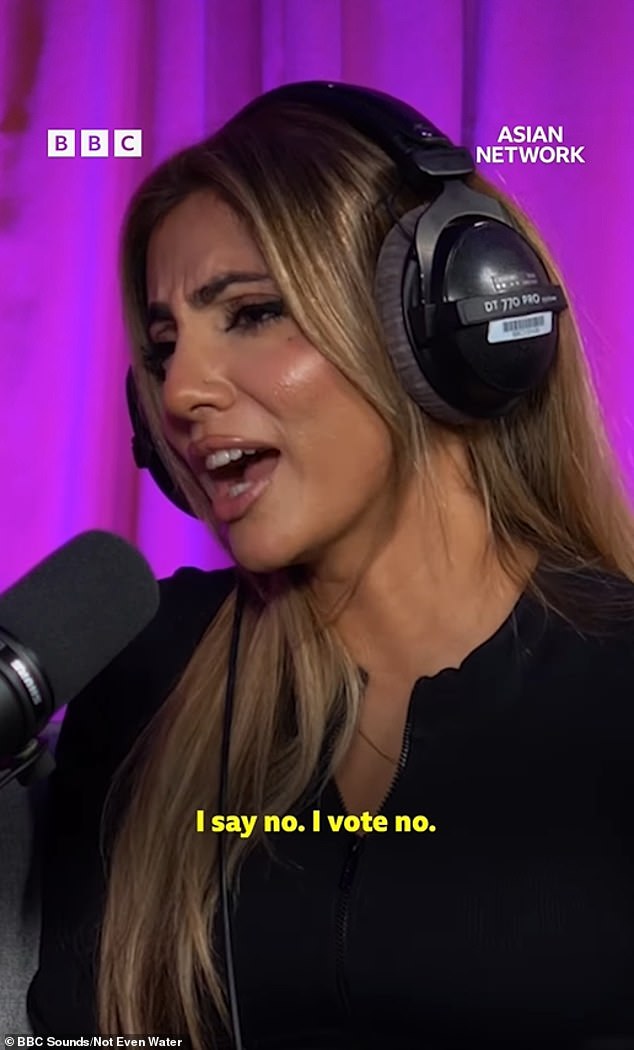
Baig said: ‘We should watch our interactions with the opposite sex, even if it is not Ramadan’


Rapper Big Zuu, who is also Muslim, also appeared on the podcast and said: “This is wrong. But you’re not the worst human being in the world if you have sex with a partner during Ramadan
In another episode of the series, Baig, who has been fasting for over 20 years, also opened up about her periods, saying she felt “guilty” about having her period during the holy month because women who menstruate are not required to fast.
Discussing the issue with guests Hodo Ibrahim and Kaltun, hosts of The Oversharers podcast, who said they had “no guilt” about having their period during the holy month, saying it was a “break” given by Allah, Baig did not agree.
The channel explained: “I promise you, not just during Ramadan, but especially during Ramadan, I feel like I’m not praying. I actually feel really bad about it.


The podcast host also said she “felt guilty” about having her period during the holy month because it prevented her from fasting.
The holy month of Ramadan for Muslims is the ninth month of the Islamic calendar and this year began on the evening of March 10 and will continue until approximately April 9.
The holy month is celebrated annually by praying during the night and abstaining from eating, drinking, and sexual acts between sunrise and sunset.