Vladimir Putin is working to raise the age limit for army officers to 70 in a bid to boost Russia’s military power, according to UK military intelligence.
If passed, the bill would be the Russian president’s latest attempt to boost his forces as Moscow’s armies continue to suffer heavy losses in Ukraine.
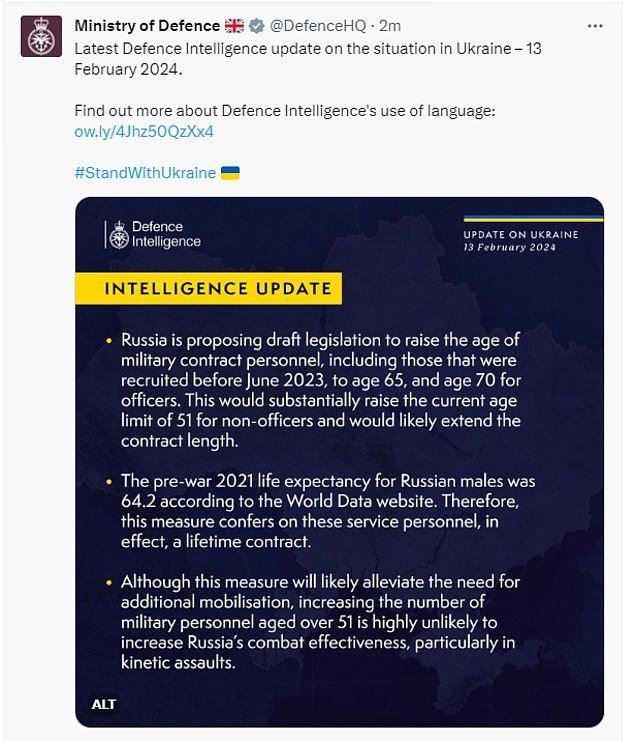
“Russia is proposing a bill to increase the age of contracted military personnel, including those who were recruited before June 2023, to 65 years and 70 years for officers,” a statement issued by the Ministry of Defense of Russia said today. Great Britain (MoD).
“This would substantially increase the current age limit of 51 for non-officers and would likely extend the length of the contract.”
Russia is believed to currently have around 1.3 million military personnel, twice as many as Ukraine’s 780,000, although not all of them are currently fighting in Putin’s war.
Although it is unclear exactly how many more troops the age increase will have in the Russian military, the figure could be significant: Nearly a third of Russia’s 146 million people are 55 years old or older.
Vladimir Putin hopes that raising the maximum age limit will help boost mobilization in his army. Pictured: An elderly soldier is seen during Russia’s 2022 partial military mobilization.

The life expectancy of Russian men was 64.2 years and that was before the war started.
However, the Defense Ministry says Putin’s plan is “unlikely” to increase the country’s military capacity, as raising the age limit by nature has a gradual, not immediate, effect.
It would mean that as the war continues, each day, more aging Russian troops who would otherwise have retired from the army are expected to continue fighting, continually increasing the army’s numbers.
The Defense Ministry statement went on to say: ‘the life expectancy of pre-war Russian men in 2021 was 64.2 years (according to the World Data Site). Therefore, this measure gives these service personnel, in fact, a lifelong contact.’
Many Russian soldiers throughout the war have fled, refusing to fight, decreasing the number of military personnel on the Russian side, something that the increase in age will help mitigate.
Ukraine is also using the removal of the age limit to increase military mobilization on its side.
The country is currently trying to pass a bill to lower the minimum age of mobilization for civilians from 27 to 25 years.
If the bill passes, it will be more difficult for civilians to avoid being drafted.
In October, Ukraine, which currently has an age limit of 60 for staff and 65 for officers, wanted to increase the maximum age limit.
His idea was to remove the age restriction completely, freeing up large numbers of older troops who wanted to fight for their country.

Elderly reservists recruited during partial mobilization are seen in 2022 attending a departure ceremony in Sevastopol, Crimea, before heading to the front (file photo)
Defense Ministry says Russia is ‘unlikely’ to increase military power
The potential increase is not the first time Putin has used age-limit removal techniques to increase the size of his military.
In May 2022, just months after Russia’s initial invasion, the 40-year-old age limit for new recruits was removed in an effort to increase numbers.
The Ministry of Defense says raising the maximum age limit will “alleviate the need for additional mobilization.”
For Putin, it is a way to grow his army without having to enlist civilians. In this way the troops will be trained and ready to fight.
In the run-up to Russia’s invasion of Ukraine on February 24, 2022, Moscow concentrated between 170,000 and 190,000 troops on the border.
However, after reaching the outskirts of kyiv, Russia suffered a series of embarrassing defeats that caused Putin’s armies to retreat from the Ukrainian capital towards the east of the besieged country.
kyiv then launched two lightning counteroffensives, pushing Russian forces even further back in both the north and south of the country, roughly to where the front lines are today.
Russia suffered devastating losses in both soldiers and equipment in the first months of the war, forcing Putin to mobilize reserves, something he had said at the beginning of his invasion he would not do.

It has been two years since Russia invaded Ukraine, with the loss of hundreds of thousands of lives.
In October 2022, Russia mobilized its 300,000 reserves to aid its war efforts.
Nine months later, in July 2023, Russia raised the maximum age for calling up reservists to 55 in another attempt to bolster their numbers.
Although exact figures on military casualties are unclear, because both Russia and Ukraine revealed little, in August the New York Times estimated that approximately 70,000 Ukrainian soldiers had died in the conflict and 120,000 Russian soldiers.
Ukrainian estimates of Russian losses are much higher.