A yoga teacher who was warned by doctors never to fly again refused to give up her dream of travel – so she spent £5,000 and two months using boats to get to New Zealand.
Bethany Hearn, from Colchester, Essex, was determined to fulfill her dream of emigrating to the other side of the world despite doctors’ warnings about the risks of flying after skull surgery.
The 23-year-old underwent surgery to remove an abnormal buildup of skin cells deep in her ear, known as cholesteatoma, in 2021.
The operation meant Bethany had part of her skull removed and her eardrum reconstructed with a cartilage graft.
However, a year after the surgery, Bethany suffered excruciating pain during a flight to Greece after the pressure on the plane caused the graft in her eardrum to sag.

Bethany Hearn spent £5,000 on boats and trains to New Zealand after doctors told her she couldn’t fly
Doctors then advised the yoga and Pilates teacher to avoid all air travel from then on to avoid further complications.
But Bethany was still determined to fulfill her wish to emigrate to New Zealand and began researching ways to reach her destination by ferry.
She said: ‘I was told not to fly again because it was too risky. The doctor said the pressure was not good for my head. He said not to fly anymore.
‘He said my graft would basically sink in further and there was a risk of my eardrum bursting.
‘But I really wanted to get back to New Zealand. I sat down and thought, “I really don’t want this to stop me from traveling.”
‘When they told me I couldn’t fly, I really didn’t want my diagnosis to define me. I just thought, “Why shouldn’t I still be able to travel?”
‘I made a joke to one of my friends that maybe he would get a boat and it all started from there. I thought why not? Surely there must be a way. In the old days, before airplanes, people still went.
Bethany’s first ferry voyage on Cunard’s Queen Mary 2 sailed from Southampton to New York on September 15, 2022.


The journey from Southampton to Auckland took almost two months. In the photo: the Bethany boat trip.


She said traveling alone on a cruise (pictured) had its own complications, including a strict dress code.


The 23-year-old underwent surgery to remove an abnormal buildup of skin cells deep in her ear, known as cholesteatoma.


The operation meant Bethany had part of her skull removed and her eardrum reconstructed with a cartilage graft.
He boarded a three-day train from New York to Los Angeles, then embarked on a Princess cruise from Los Angeles, stopping in Hawaii, Fiji and French Polynesia along the way, before finally arriving in New Zealand on October 27. .
The trip lasted almost two months and cost Bethany around £5,000, but she plans to do it again in June this year for an epic trip back to the UK after living in Auckland, New Zealand, for the past 16 months.
Bethany said she was the youngest person aboard her first cruise for “50 years,” and passengers were confused about what the backpacker was doing aboard the ship.
She also faced a number of problems as a solo female traveler, including men calling her room on the cruise and others finding her profiles on social media.
He continued: ‘The first leg of the journey was quite lonely. I was the youngest passenger by about 50 years. The cruise was really great though – I went to a lot of fitness classes and the entertainment was fun.
“I felt a lot of hostility. I think people were confused about what I was doing on the boat. I didn’t have nice clothes, I just had my backpack. But I met two other really nice solo travelers.
After a three-day cross-country train ride and another cruise across the Pacific Ocean, Bethany arrived in New Zealand with $40 to her name.
There, she worked as a nanny and in hospitality before becoming a yoga and Pilates teacher.
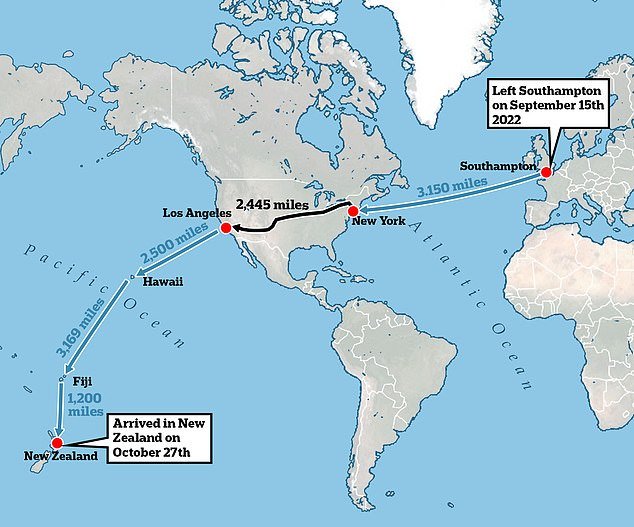
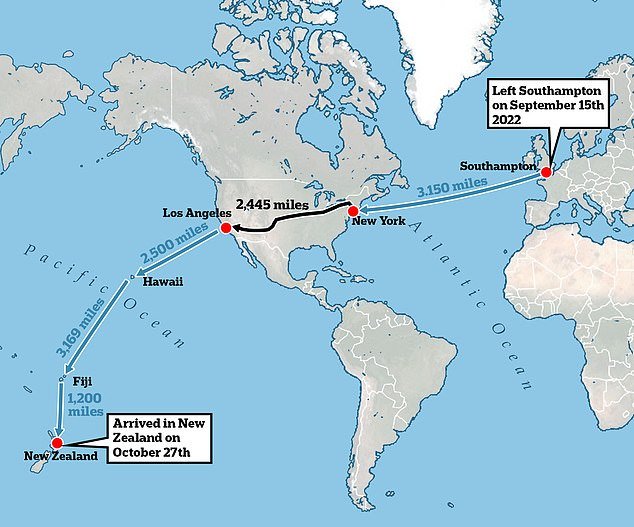
Bethany’s total trip across the United States was more than 12,000 miles via a combination of trains and ferries.


Bethany currently works as a yoga and pilates teacher in Auckland.




She was forced to take a more unusual and expensive route to New Zealand because she was determined not to give up on her dream.


Bethany’s first ferry voyage on Cunard’s Queen Mary 2 sailed from Southampton to New York on September 15, 2022.
Bethany said: ‘I had saved £6,500 to get to New Zealand and actually turned up with $40 to my name. I got here and immediately started working.’
Bethany said her unconventional method of traveling the world helped her “define who she is” and she plans to make the same mammoth trip home next month.
Bethany said: ‘I really underestimated myself. You realize that life is short, the world is huge. I look back and think, “Thank God I got on that boat.”
‘It was hard to do it alone, but it really defined who I am.
‘It’s a great way to explore the world and a lot of fun. The cost is the only thing to consider, but it was much more reasonable than initially anticipated.’
A one-way flight from London to Auckland, New Zealand costs between £400 and £800 and takes a minimum of 24 hours, including at least one stopover.