A board-certified dermatologist has revealed how much hair you can lose before it indicates there is a problem.
Mississippi-based Dr. Lindsey Zubritsky shared the information in a recently resurfaced video which was posted on his TikTok account in February.
The dermatologist, better known as @dermguru On social media, she often posts videos in which she shares various tips for skin and hair health.
In this clip, Dr. Zubritsky presented a numbered chart showing the scale of hair loss and what it looks like in real terms.
Board-certified dermatologist Dr. Lindsey Zubritsky has revealed how much hair you can lose before it becomes a cause for concern.
Dr. Lindsey Zubritsky, better known as @dermguru on social media, based in Mississippi, often makes videos sharing various tips for skin and hair health.
‘Did you know that it’s actually normal to lose between 100 and 200 hairs every day?’ Zubritsky began in the video, which has so far reached more than two million views.
In the graph, I had measured hair loss at different degrees. However, he noted that it can look different depending on the length of your hair.
Grade one was classified into ten hairs, grade two into 50 hairs, grade three into 100 hairs, grade four into 200 hairs, grade five into 400 hairs, and grade six into 750 hairs.
“If your hair looks like any of these, it’s normal,” he said, pointing to hair loss grades one through three.
“If your hair starts to look like this, about four hundred hairs, or this, about seven hundred and fifty hairs, you have a problem,” he shared.
According American scientistThe average person has between 90,000 and 150,000 hairs on their head.
So while the idea of losing 100 hairs a day may seem like a lot, it isn’t much in the grand scheme of things.
But, if you’re losing more than that, Dr. Zubritsky recommended contacting your dermatologist to schedule an appointment to discuss possible courses of treatment.

In this clip, Dr. Zubritsky presented a numbered chart showing a scale of hair loss and what it looks like in real terms.

In other videos, the dermatologist has also recommended products like Nutrafol, which is a popular hair growth supplement, and even rosemary oil.
Treatment for hair loss can range from taking a medication such as Rogaine, biotin, zinc or collagen, to procedures such as platelet-rich plasma (PRP) therapy or phototherapy, depending on Cleveland Clinic.
In other videos, the dermatologist also recommended products like Nutrafol, which is a popular oral hair growth supplement, and even rosemary oil.
Rosemary oil has gained traction as a natural remedy to prevent hair loss and promote growth in recent months.
However, the dermatologist did observe in a February TikTok Video It is important to use rosemary oil in the correct way.
Dr. Zubritsky recommended using the oil twice a day for at least six months and applying it directly to the scalp.
He said the oil should not be mixed with shampoo and should be used more than one to three times a week.
“If you’ve been using rosemary oil once or twice a week and you’ve only been using it for two or three months, and you haven’t noticed any results, it’s because you’re not doing it right,” she said in the TikTok clip.
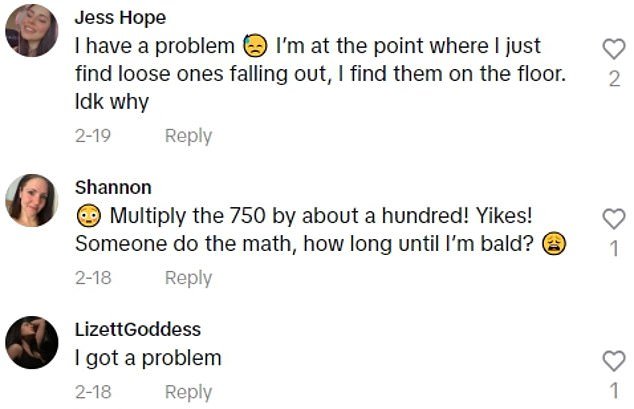
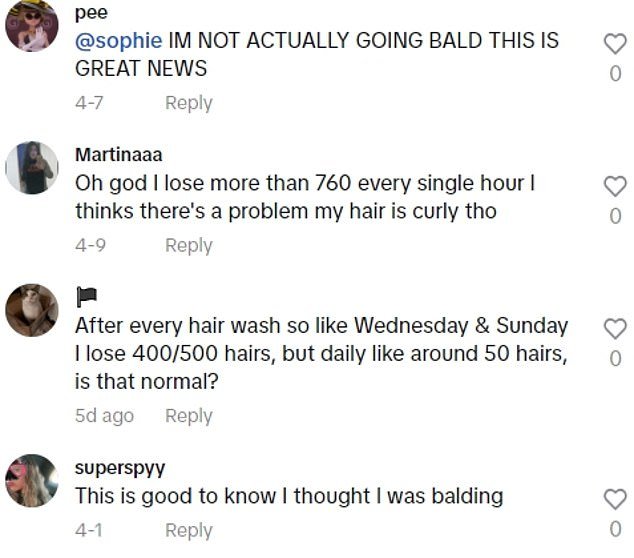
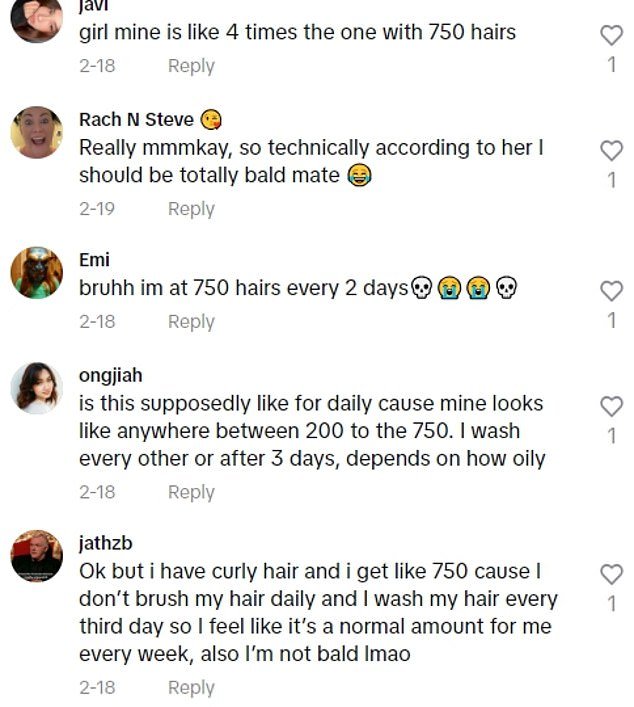
In the comments section of Zubritsky’s video, many users admitted that they struggled with hair loss, proving that it is not an uncommon problem.
“You should use it twice a day and wait six to nine months before deciding whether it’s working for you or not.”
In the comments section of Zubritsky’s video, many users admitted that they struggled with hair loss, proving that it is not an uncommon problem.
‘I’m not lying… I’ve been losing a LITERAL fist full of hair over the last month. What’s wrong with me?’ wrote one person.
Another user agreed: “I’m losing about twice as much as the last image every morning and night and I don’t know what to do.”
“Good to know I thought I was going bald,” someone else shared.